Critical Infrastructures vulnerable to IOCONTROL Malware >>>
A newly identified malware strain dubbed “IOCONTROL” has emerged as a critical threat to operational technology (OT) and Internet of Things (IoT) systems, particularly targeting fuel-management infrastructure in the United States and Israel.
First observed in December 2024, this Linux-based malware has been linked to the pro-Iranian hacktivist group Cyber Av3ngers, which has historically pursued anti-Israeli cyber campaigns.
Initial attacks leveraged compromised credentials—part of a broader 33% year-over-year surge in credential theft—to infiltrate critical systems, enabling threat actors to establish persistent remote access, manipulate industrial processes, and exfiltrate sensitive operational data.
Flashpoint analysts identified IOCONTROL’s modular architecture, which combines UPX-packed binaries, encrypted command-and-control (C2) communications, and surveillance capabilities tailored for resource-constrained IoT environments.
The malware primarily exploits vulnerabilities in internet-exposed industrial control systems (ICS), using the MQTT protocol—a lightweight messaging standard common in IoT ecosystems—to bypass traditional network monitoring tools.
Its deployment in attacks against fuel distribution networks underscores escalating risks to critical infrastructure amid heightened geopolitical tensions in the Middle East.
Technical Overview and Persistence MechanismsIOCONTROL employs sophisticated evasion tactics, starting with a modified UPX packer that alters binary magic values to hinder static analysis.
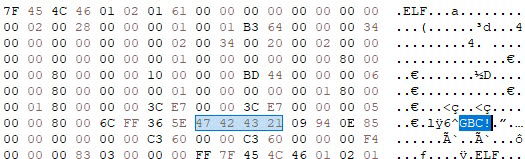
While standard UPX utilities fail to unpack the malware due to these alterations, Flashpoint researchers demonstrated that restoring the magic bytes (00 00 00 00 00 00 00 02 00 34 00 20 00 02 00 34) enables successful decompression.
Once executed, the malware unpacks itself in memory and establishes persistence through a multi-stage process:-
Directory Creation: IOCONTROL creates two directories—/tmp/iocontrol/ and /etc/rc3.d—with full read, write, and execute permissions. These serve as operational hubs for staging payloads and maintaining persistence across reboots.Startup Script Injection: A bash script is written to /etc/rc3.d/S99iocontrol, ensuring execution at system startup. The script includes watchdog functionality to restart the malware if terminated:#!/bin/sh/usr/bin/iocontrol >/dev/null 2>&1 &while true; do if ! pgrep -x "iocontrol" >/dev/null; then /usr/bin/iocontrol >/dev/null 2>&1 & fi sleep 60doneThis mechanism ensures continuous operation even if security tools interrupt initial execution.
C2 Communication: The malware resolves its C2 server’s IP via a DNS query to CloudFlare, extracting the Answer[data] field from the response. It then establishes an MQTT connection to the broker, transmitting beacon packets containing system metadata (kernel version, hostname, time zone) encrypted using AES-256-CBC. The encryption key derives from environment variables 0_0 and 0_1, set during execution, which store hashed GUID values split into key and initialization vector (IV) components.IOCONTROL’s blend of IoT-focused protocols and credential-based initial access vectors presents unique challenges for defenders.
Flashpoint’s investigation revealed attempts by the malware’s developer to sell it on underground forums like BreachForums, signaling potential proliferation across threat actor groups.
Organizations managing OT environments must prioritize firmware patching, network segmentation, and anomaly detection for MQTT traffic to mitigate risks posed by this evolving threat.