Critical Vulnerability from Verizon Call Filter App >>>
A security vulnerability in the Verizon Call Filter iOS app allowed attackers to potentially leak the call history logs of Verizon Wireless customers. The vulnerability allowed unauthorized access to call logs, which contain valuable metadata.
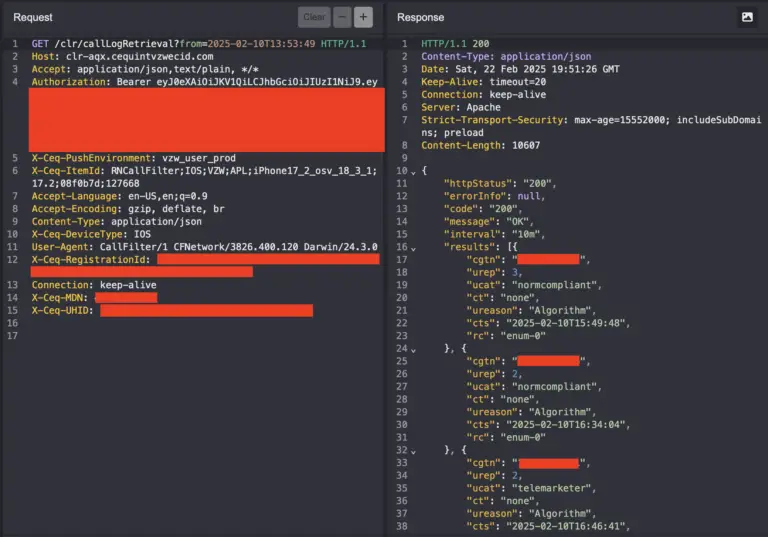
The Verizon Call Filter app retrieves recent call history by sending a network request to a server. This request includes details like the user’s phone number and the time period for the call records. However, the application failed to validate if the phone number in the request matched the signed-in user’s number.
According to security researcher Evan Connelly, “It was possible to modify the phone number being sent, and then receive data back for Verizon numbers not associated with the signed in user.” This flaw allowed anyone to lookup call data for any Verizon number.
The unauthorized access to call logs raises significant privacy and safety concerns. As the report states, “Consider scenarios involving survivors of domestic abuse, law enforcement officers, or public figures—individuals who rely on the confidentiality of their communication patterns.” The exposure of call logs can lead to the reconstruction of daily routines, identification of contacts, and inference of personal relationships.
The Verizon Call Filter app uses the endpoint https://clr-aqx.cequintvzwecid.com/clr/callLogRetrieval to retrieve call history. The request requires a JSON Web Token (JWT) in the Authorization header and uses an X-Ceq-MDN header to specify the phone number. The vulnerability lies in the fact that “the /clr/callLogRetrieval endpoint was not validating that the phone number specified in the X-Ceq-MDN header matches the sub in the JWT payload,” which allowed the retrieval of call history logs for any phone number.
The researcher believes that the vulnerability affected a large portion, if not all, Verizon Wireless customers with the Call Filter service enabled. While the endpoint only returned received calls, it could still provide a substantial amount of information, and even a partial view of outgoing calls to other Verizon customers.
The report suggests that the vulnerability may have resided in a server owned by Cequint, a telecom technology company specializing in caller ID services. The domain name hosting the API, CEQUINTVZWECID.COM, and information from Crunchbase, point to Cequint’s possible involvement. This raises questions about the extent of data held by Cequint and its security measures.
Verizon confirmed issue was resolved.