Gootloader Malware Latest Campaign Analysis >>>
GootLoader is an initial-access-as-a-service malware that operates by delivering the GootKit banking trojan and other malicious payloads. It utilizes techniques such as fileless execution and process injection to avoid detection. The malware is often distributed through SEO poisoning and compromised websites, deceiving users into downloading infected files.
GootLoader is a loader malware initially designed to distribute the GootKit banking trojan. Operated by the UNC2565 threat group, today it functions as initial-access-as-a-service software, catering to cybercriminals who aim to deploy their malware, like Cobalt Strike, on already infected machines. While GootKit has been in circulation since 2014, GootLoader was introduced more recently in 2021. Campaigns involving GootLoader target users visiting hijacked WordPress websites and online forums. Attackers inject malicious code into these pages, deceiving visitors into downloading fake legal documents, which, in reality, turn out to be malicious files designed to infect their systems of GootLoader.
The notorious Gootloader malware has reemerged with evolved tactics, now leveraging Google Search advertisements to target users seeking legal document templates.
This sophisticated campaign specifically promotes “free” legal templates, primarily non-disclosure agreements, through sponsored search results that appear legitimate to unsuspecting users.
Upon clicking these advertisements, victims are directed to lawliner[.]com where they are prompted to enter their email address to receive the requested document.
The attack chain begins innocuously with users searching for terms like “non disclosure agreement template” and encountering sponsored ads from domains that appear to offer legitimate legal services.
These advertisements are reportedly being delivered through “MED MEDIA GROUP LIMITED,” which security experts believe may have been compromised to facilitate this campaign.
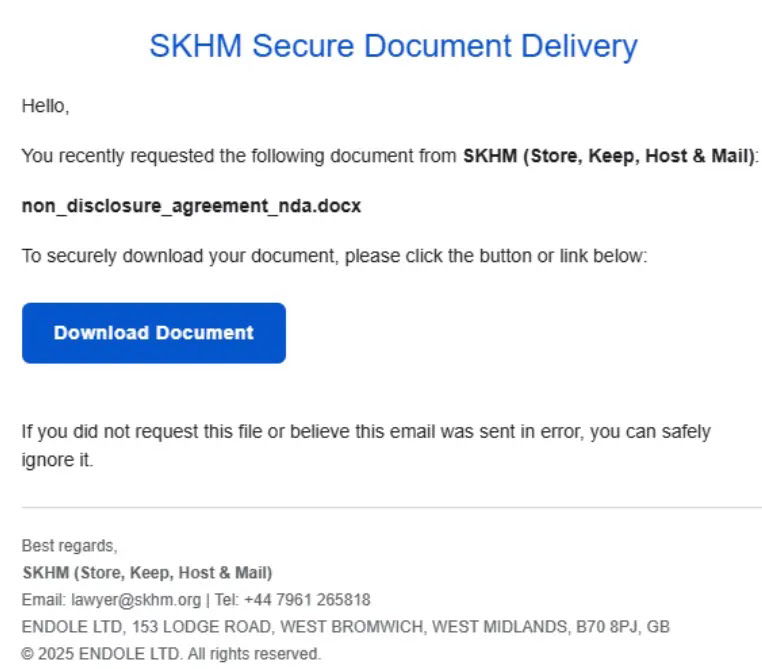
A security analyst identified that after submitting their email address, victims receive a message from lawyer@skhm[.]org containing a download link that purportedly leads to the requested document.
However, instead of receiving a legitimate .docx file, users unwittingly download a compressed JavaScript file disguised as the legal document they requested.
The infection mechanism demonstrates sophisticated social engineering techniques.
When executed, the malicious JavaScript creates a scheduled task pointing to another .JS file in the user’s AppData\Roaming folder.
This persistence mechanism ensures the malware remains active across system reboots.
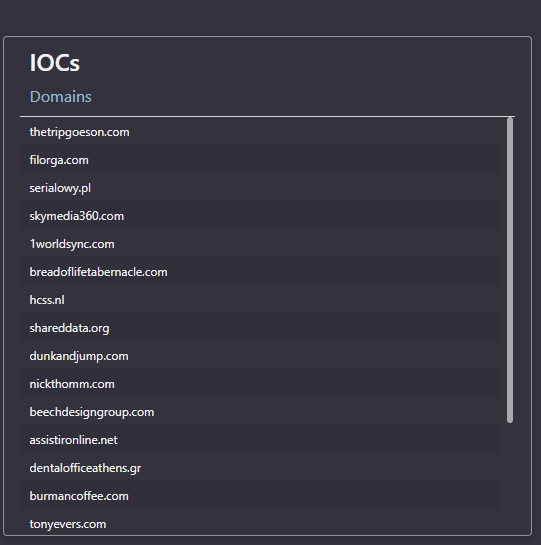
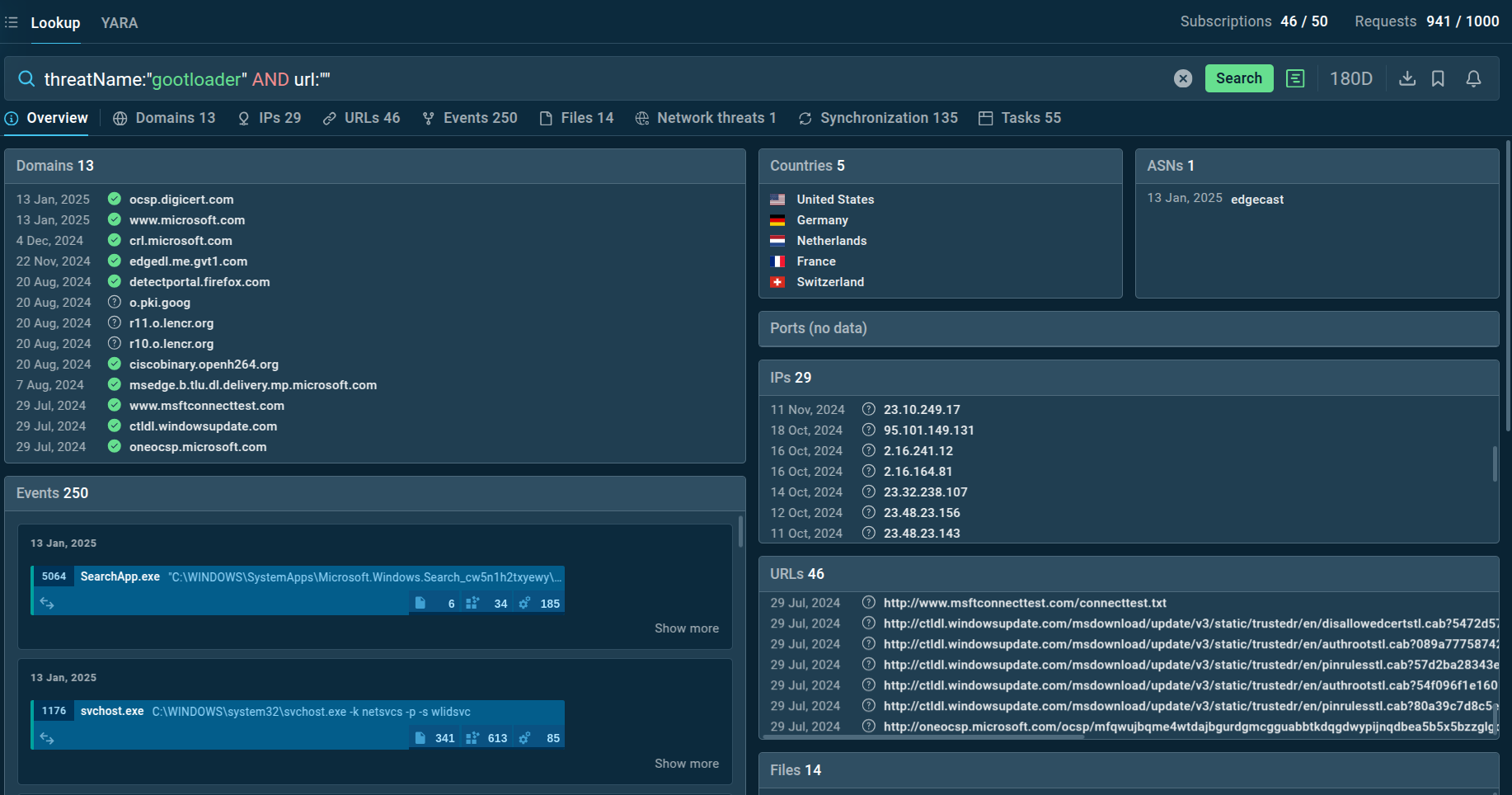
The script then executes PowerShell commands to establish connections with multiple WordPress blogs, approximately 10 in total, with 1-2 being genuinely compromised servers while others serve as decoys to complicate analysis.
Security professionals recommend implementing immediate security measures including blocking web traffic to lawliner[.]com and skhm[.]org, filtering email communications from skhm[.]org, and conducting retrospective threat hunting for any historical interactions with these malicious domains to identify potentially compromised systems within organizational networks.
GootLoader malware technical details >>>>
GootLoader employs a multi-stage execution process, characterized by several advanced capabilities:
Memory-only execution: The second stage of GootLoader deploys entirely in memory without writing to disk, making it difficult for traditional antivirus solutions to detect.Encryption and obfuscation: The malware utilizes encryption and obfuscation techniques to conceal its activities and avoid detection by security tools.External payload fetching: The second-stage payload is typically fetched from an external URL hardcoded in the malware, ensuring that the malicious code is not stored locally on the infected machine. See how you can easily extract hardcoded data with the ANY.RUN sandbox.Evasion techniques: GootLoader performs evasion by sleeping, which helps it avoid detection by delaying its activities and blending in with legitimate processes.Persistence mechanisms: To ensure it remains active on the infected system, GootLoader modifies the registry and adds an autorun entry, allowing it to execute automatically on system startup.Process injection: The malware uses process injection to hijack legitimate Windows utilities with malicious code, further complicating detection and analysis.Malware deployment: GootLoader is capable of dropping various types of malware, including GootKit and Cobalt Strike, expanding its potential for damage and data exfiltration.Lateral movement: The latest versions of GootLoader are equipped with the ability to move laterally within a network, spreading the infection to other connected devices.
GootLoader execution process >>>
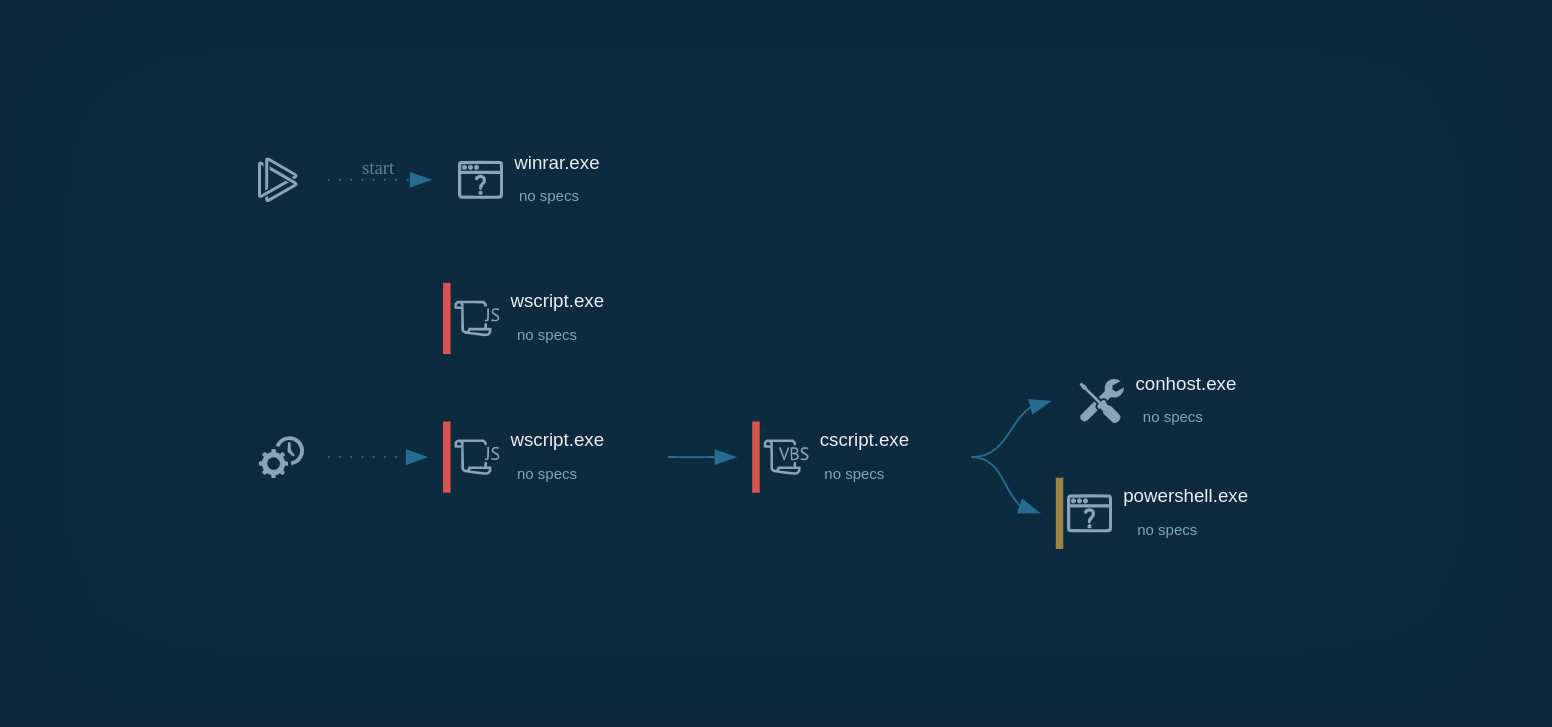
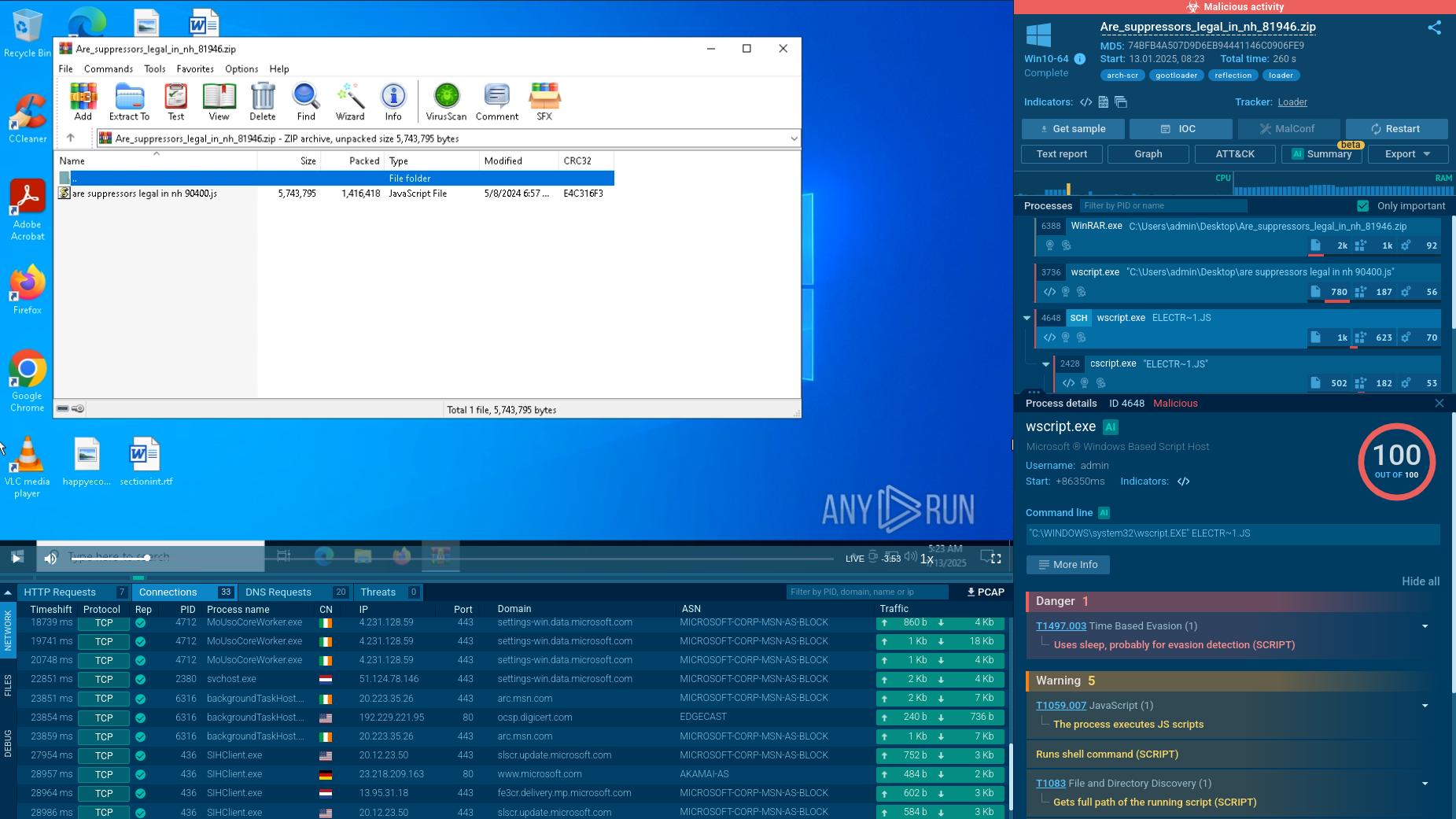
GootLoader's infection process involves several steps. It usually starts when someone visits a compromised website and downloads a malicious archive, often disguised as a legitimate document like a template or contract. This archive typically contains a JavaScript file.
When the file is opened, the first stage of infection begins. It uses Windows Script Host (wscript) to run an obfuscated JavaScript payload. This payload creates a scheduled task to ensure the infection persists, leading to the execution of a second obfuscated JavaScript file stored on the disk.
In the second stage, the execution shifts from wscript to cscript, which runs as a child process. This allows a PowerShell script to run, further deobfuscating and executing more malicious code. The PowerShell script collects information from the infected system, such as operating system details, running processes, and environment variables. It can also check the system's location and use sleep commands. The collected information is then compressed, encoded, and sent to a command-and-control (C2) server.
The third stage involves executing additional payloads, which might include components like a Cobalt Strike beacon or other malware. These payloads are often written into Windows Registry keys to ensure they persist and remain active even after the system is rebooted. GootLoader's use of obfuscation techniques makes it hard for traditional security methods to detect. Its sophisticated infection process highlights its effectiveness as a persistent threat to enterprise environments.