Kentico Xperience CMS RCE Vulnerability >>> <CVE-2025-2748>
A critical security flaw in Kentico Xperience CMS, a widely used enterprise content management system (CMS), has been uncovered. By exploiting a Cross-Site Scripting (XSS) vulnerability, attackers can execute remote code.
This vulnerability, tracked as CVE-2025-2748, affects versions of Kentico Xperience up to 13.0.178 and has significant implications for organizations relying on the platform.
Kentico Xperience CMS Vulnerability -
According to watchTowr, the vulnerability arises from a combination of two flaws within Kentico Xperience CMS:
Unauthenticated Resource Fetching HandlerThe /CMSPages/GetResource.ashx endpoint allows unauthenticated users to fetch resources like images or scripts. While it enforces a whitelist of file extensions, it permits SVG files, which can contain embedded JavaScript code.
When such files are retrieved with the MIME type image/svg+xml, browsers execute the embedded JavaScript, leading to XSS.
Temporary File Upload PrimitiveThe /CMSModules/Content/CMSPages/MultiFileUploader.ashx endpoint enables unauthenticated file uploads to a temporary directory within the webroot.
Although the upload functionality restricts file extensions to a predefined list (e.g., .png, .jpg), attackers can bypass this by uploading a ZIP archive containing an SVG file.
Kentico’s custom file handler processes ZIP files, allowing attackers to extract and execute malicious SVG files stored within.
Exploitation ChainThe exploitation involves chaining these vulnerabilities:
Crafting Malicious Files: Attackers create an SVG file containing JavaScript payloads and package it into a ZIP archive.
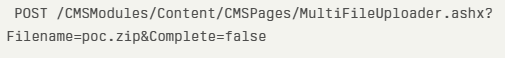
Uploading ZIP File: Using the MultiFileUploader endpoint, the attacker uploads the ZIP file to a predictable temporary directory.
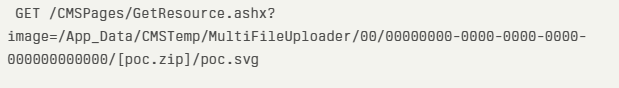
Triggering XSS: The attacker uses the GetResource handler to retrieve the malicious SVG file from the uploaded ZIP archive. The browser executes the embedded JavaScript when accessing this file.
Post-Authentication Remote Code Execution (Optional): If attackers gain administrative access through other means (e.g., exploiting authentication bypass vulnerabilities like CVE-2025-2746), they can modify allowed file extensions and upload server-side executable files, such as .aspx, enabling full remote code execution.
Proof-of-concept (PoC) Exploit -->
A proof-of-concept (PoC) exploit demonstrates how an attacker can achieve XSS:
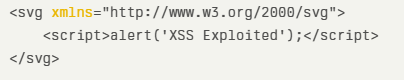
Create an SVG file with embedded JavaScript
Package it into a ZIP archive (poc.zip) and upload using post request.
Access the malicious SVG via GET request.
Upon execution, the browser displays an alert box with “XSS Exploited,” proving successful exploitation. This vulnerability poses severe risks, including unauthorized access to sensitive data, session hijacking, and complete server compromise through remote code execution.
Organizations using affected versions of Kentico Xperience CMS are urged to upgrade to version 13.0.178 or later, which has been patched for these issues.