Plantronics Hub Privilege Escalation Vulnerability >>>
A critical security vulnerability in Plantronics Hub software enables attackers to escalate privileges through an unquoted search path weakness.
Affecting versions 3.24.5 through 3.25.2, this vulnerability becomes particularly dangerous when installed alongside OpenScape Fusion for MS Office, which is often configured as a startup application on corporate systems.
The flaw exploits Windows’ handling of unquoted paths containing spaces.
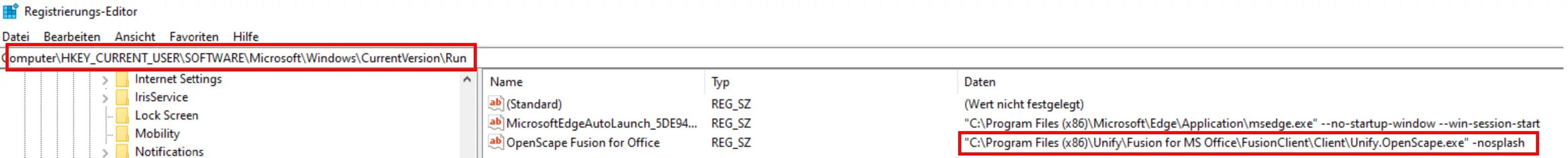
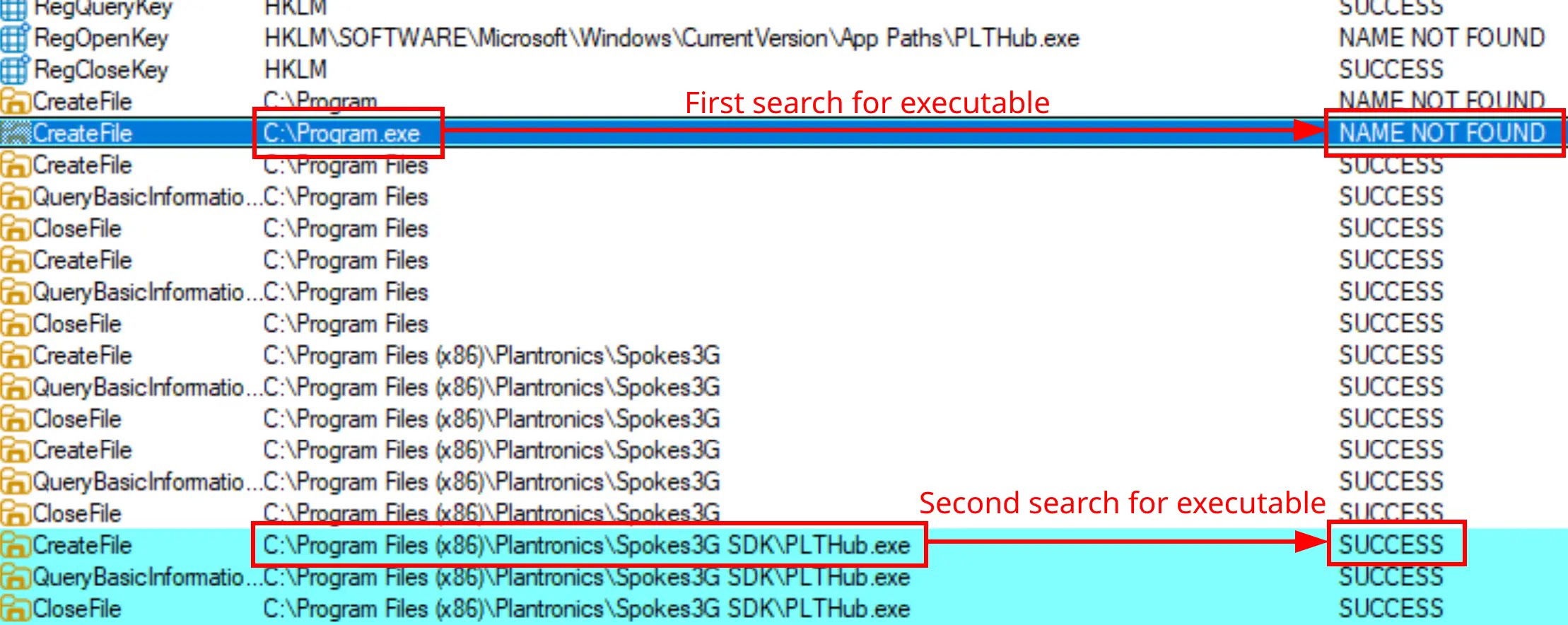
When OpenScape attempts to launch Plantronics Hub using the path C:\Program Files (x86)\Plantronics\Spokes3G SDK\PLTHub.exe stored in the registry, Windows first tries to execute C:\Program.exe before attempting the full path.
This behavior creates a perfect attack vector if users have write permissions to the C:\ directory.
8Com researchers identified that attackers can exploit this behavior by placing malicious files in the C:\ directory, which would then execute with elevated privileges when an administrator runs OpenScape.
This vulnerability is classified as CWE-428: Unquoted Search Path or Element, a known weakness where applications fail to properly quote paths containing spaces.
The attack requires three components in the C:\ directory: Program.exe (entry point), aka.exe (UAC bypass), and ape.exe.lnk (payload).
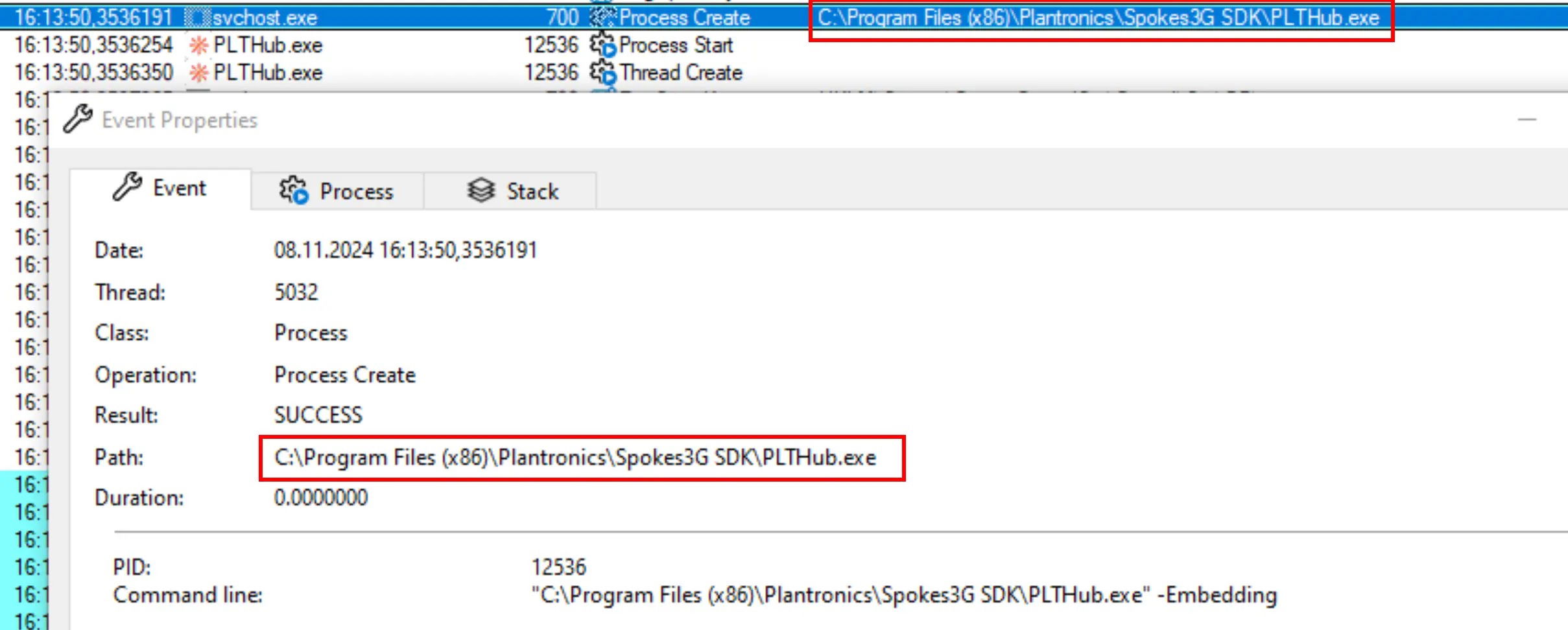
The exploitation occurs when OpenScape launches at startup and attempts to start the Plantronics Hub, triggering the execution chain that results in privilege escalation.
Infection Mechanism DetailsThe technical implementation relies on the LocalServer32 registry key that contains the unquoted path to PLTHub.exe.
When executed, Program.exe calls aka.exe with specific parameters to bypass User Account Control restrictions and execute the payload with administrative privileges.
For demonstration purposes, 8Com researchers used a simple PowerShell command as the payload:-
powershell.exe -c "whoami /all > C:\poc.txt"This command, when executed with administrative privileges, writes the current user’s elevated permissions to a text file, confirming successful privilege escalation.
The process begins when an administrator logs in, automatically triggering OpenScape Fusion which attempts to launch Plantronics Hub through the vulnerable path.
No patch is available as Plantronics Hub is no longer officially supported by HP.
Security professionals should mitigate this risk by either quoting the registry path or restricting write permissions to C:\, ensuring only administrators can modify the root directory.
HP has updated their End of Commercial Sale Notice to inform customers about this vulnerability.