PostgreSQL Servers Compromised >>>
A new report from Wiz Threat Research reveals a rapidly evolving malware campaign that has silently infected over 1,500 cloud-hosted PostgreSQL servers, deploying fileless cryptominers under the radar of traditional security tools. At the center of the operation is CPU_HU, a Golang-based miner, dropped and executed entirely in memory to evade detection.
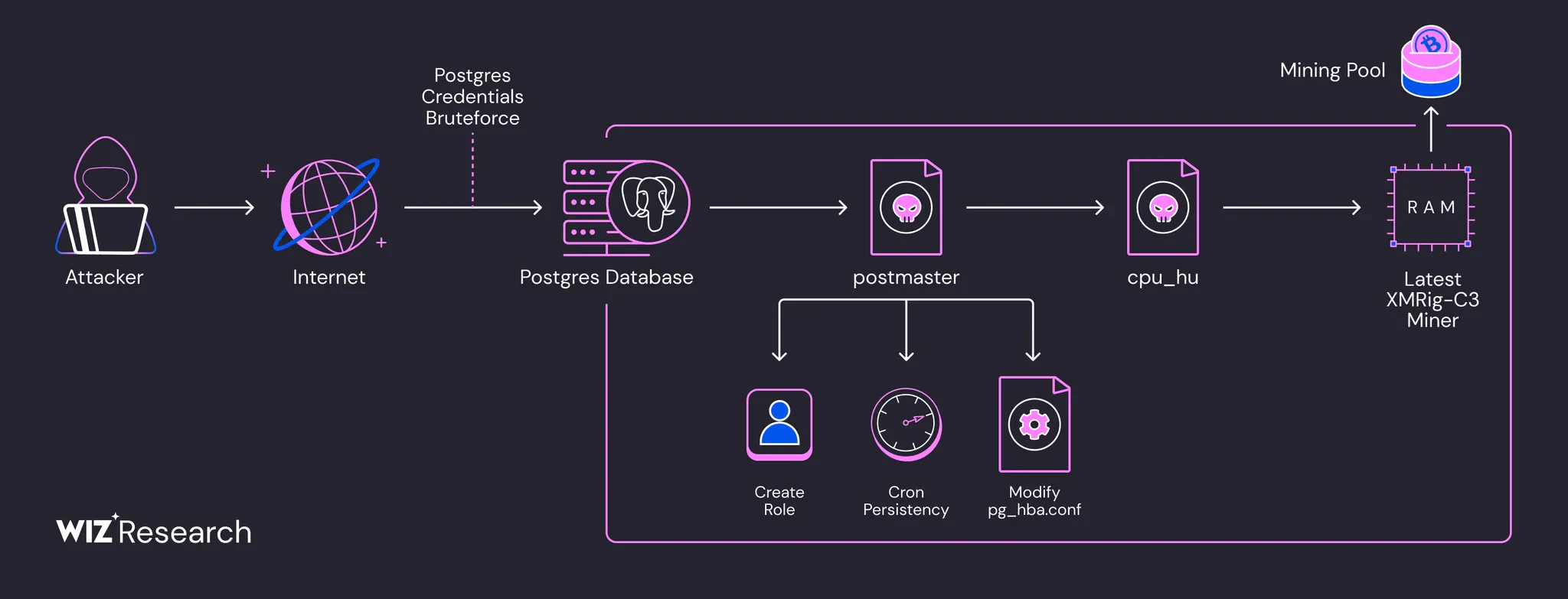
The campaign, attributed to a threat actor tracked as JINX-0126, leverages default credentials and misconfigured PostgreSQL settings to remotely execute code, deploy custom loaders, create stealthy backdoors, and mine cryptocurrency using compromised cloud resources.
“Misconfigured PostgreSQL instances are highly common, providing a low hanging fruit entry point for opportunistic threat actors to exploit,” Wiz researchers explain.
JINX-0126 begins by scanning the internet for publicly exposed PostgreSQL servers configured with weak or default login credentials. Once authenticated, the actor abuses the COPY … FROM PROGRAM SQL function, which enables command execution directly from the database.
“Threat actors are actively scanning the network for weakly configured services… with PostgreSQL being a frequent target,” the report confirms.
This method grants attackers remote access to dropper scripts and loader binaries, initiating the infection chain. Once inside, the actor downloads and executes a binary named postmaster, crafted to mimic the legitimate PostgreSQL multiuser daemon.
The binary is:
Written in GoPacked with a modified UPX packerAppended with an encrypted configuration trailer containing victim details and the attacker’s mining wallet“The postmaster binary will execute itself with the command line postgres: replication launcher as an attempt to blend within the service,” notes Wiz.
For persistence, postmaster:
Adds itself to a cronjob to relaunch every minuteModifies the PostgreSQL access config (pg_hba.conf) to lock out legitimate usersDrops SSH keys and creates a new superuser psql_sys with hardcoded credentials for backdoor accessTo weaken defenses and ensure control, the attacker:
Alters the admin user to remove its superuser rightsCreates a high-privilege backdoor role using the CREATE ROLE SQL command“This allows the attacker to later log in to the system even if the password has been changed.”
Once the system is secured, the loader drops the cpu_hu binary—a fileless cryptominer also built in Golang and packed with a modified UPX. This payload:
Contains base64-encoded mining configuration embedded in its trailerDownloads the XMRig-C3 binary from a public GitHub repoCreates a fake config file under /tmp/Executes the miner via memfd, keeping it memory-resident and deleting itself from disk“The attacker appends unique configuration data to malware samples, so the file hash of cpu_hu and postmaster varies between victims,” making signature-based detection ineffective.
Wiz researchers uncovered three wallets linked to JINX-0126, each with approximately 550 workers connected to the C3Pool mining service, suggesting a minimum of 1,500 infected machines in the wild.
The miner config includes:
Wallet addressWorker IDPostgreSQL server credentialsIP address of the compromised hostJINX-0126’s CPU_HU campaign exemplifies the rising trend of fileless, cloud-native malware that exploits poor configuration rather than complex exploits.