SvcStealer Malware Exploiting Users To Steal Sensitive Data From Browsers & Apps
A sophisticated new information stealer dubbed SvcStealer 2025 has emerged, targeting sensitive user data through spear phishing email attachments.
First observed in late January 2025, this malware harvests extensive personal and financial information from infected systems, including machine data, installed software, user credentials, cryptocurrency wallets, and browser data.
The malware employs a methodical approach to data theft, systematically extracting information from various applications before compressing it and exfiltrating it to command and control (C2) servers.
After successful data collection, SvcStealer can potentially download additional malware payloads, expanding its threat capabilities beyond initial data theft.
SEQRITE researchers identified this threat during routine threat hunting operations, noting that the malware is written in Microsoft Visual C++ programming language.
Analysis revealed that SvcStealer implements evasive techniques by terminating monitoring processes and deleting traces of its activities to avoid detection by security tools.
Infection Analysis >>>
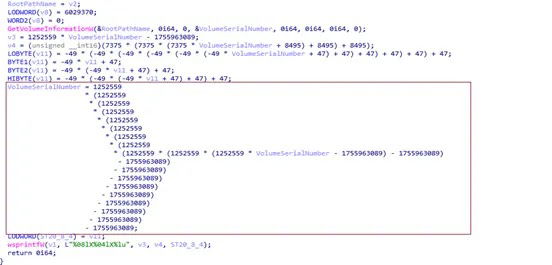
Upon infection, the malware generates a unique 11-byte alphanumeric value derived from the victim’s volume serial number through arithmetic operations.
This value serves as an identifier for the compromised system and helps ensure only one instance of the malware runs at a time.
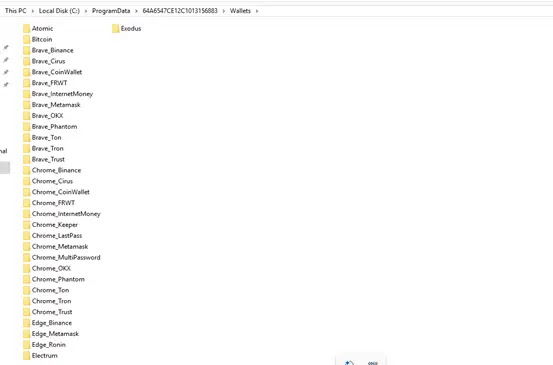
SvcStealer’s data exfiltration mechanism reveals its sophisticated design. After collecting sensitive information, the malware stores data in the ProgramData directory under the uniquely generated folder name.
It targets specific applications including cryptocurrency wallets from multiple browsers (Chrome, Edge, Brave), messaging platforms (Telegram, Discord), and captures credentials from various browsers.
The malware also takes screenshots and collects system information including running processes.
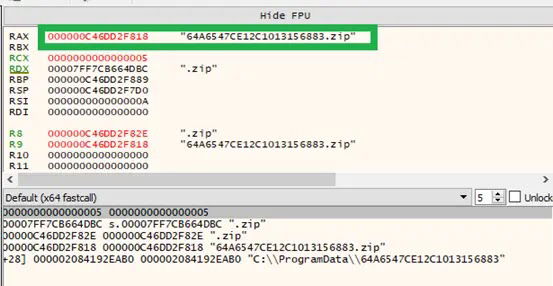
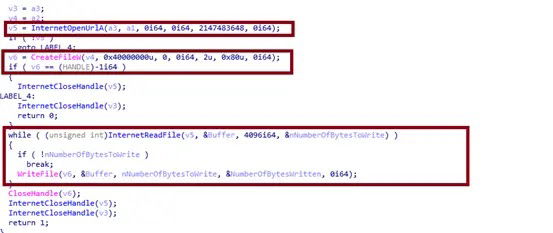
Here the SvcStealer compresses the folder into a zip file and establishes a connection to its C2 servers (185.81.68.156 or 176.113.115.149) on port 80.
Using HTTP POST requests with a Content-Type of “multipart/form-data,” the malware transmits the stolen data disguised as normal web traffic.
To maintain persistence, the malware continues to beacon to its C2 server, awaiting further commands which may include downloading additional malicious payloads.
Security experts recommend vigilance against suspicious email attachments and implementing advanced endpoint protection to defend against this emerging threat.