Veeam Backup & Replication RCE Vulnerability CVE-2025-23120 >>>
A remote code execution (RCE) vulnerability in Veeam Backup & Replication could allow any domain user to compromise backup servers with SYSTEM-level privileges.
The findings, assigned CVE-2025-23120, affect Veeam Backup & Replication 12.3.0.310 and all earlier version 12 builds, demonstrating how blacklist-based security mechanisms continue to fail in enterprise environments.
Veeam Deserialization Flaws -
According to watchTowr Labs Report, the vulnerabilities leverage flawed deserialization mechanisms within Veeam’s backup solution, allowing attackers to escalate privileges and potentially compromise critical backup infrastructure.
Most concerning is the authentication barrier – any user belonging to the local Users group on a Windows host running Veeam, or any domain user if the server is joined to Active Directory, can exploit these vulnerabilities.
“Imagine that any employee of your 50,000 people organization can get SYSTEM on your backup server. Kind of scary, right?” researchers noted, emphasizing how this design flaw creates an enormous attack surface.
The security flaws stem from Veeam’s implementation of a blacklist-based protection mechanism for its .NET BinaryFormatter deserialization process.
The researchers identified two distinct gadget chains – labeled WT-2025-0014 and WT-2025-0015 – that bypass these protections.
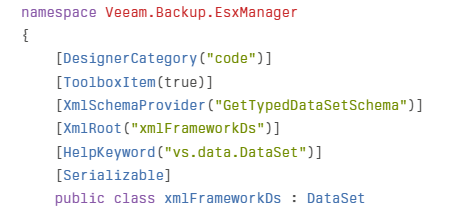
The first vulnerability (WT-2025-0014) exploits the Veeam.Backup.EsxManager.xmlFrameworkDs class, which inherits from the dangerous DataSet class:
The second vulnerability (WT-2025-0015) similarly abuses the Veeam.Backup.Core.BackupSummary class, which also extends the DataSet class known for RCE capabilities.
Authentication and Access Vector -
The attack vector becomes particularly concerning when examining the authentication mechanisms.
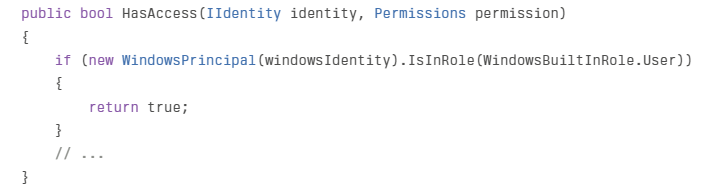
Researchers discovered that Veeam Mount Service implements access checks in the CMountServiceAccessChecker.HasAccess method:
This code grants access to any member of the Windows built-in Users group. In domain-joined environments, all domain users are automatically added to this group, making this vulnerability exploitable by any domain user.
Following previous vulnerability discoveries, Veeam added entries to their blacklist file (Veeam.Backup.Common.Sources.System.IO.BinaryFormatter.blacklist.txt).
However, security experts emphasize that blacklist-based approaches to deserialization security are fundamentally flawed and can never be comprehensive enough.
Recommendations -
Security experts advise immediate patching of affected Veeam installations. Organizations using Veeam should:
Apply the latest security updates from VeeamConsider restricting domain user access to backup serversRe-evaluate the decision to join backup servers to Active Directory domainsImplement network segregation for backup infrastructureThis vulnerability highlights the ongoing challenge in secure software design, particularly in backup solutions that have become primary targets for ransomware operators seeking to disable recovery capabilities.